 The Enigma Protector is a powerful tool designed for complex protection of program modules. Program modules include the following types of objects:
The Enigma Protector is a powerful tool designed for complex protection of program modules. Program modules include the following types of objects:
- Win32 and Win64 Portable Executable Files (*.exe);
- Dynamic Link Libraries (*.dll);
- .NET Executables (*.exe).
- Windows Screen Saver Files (*.scr);
- ActiveX Component Files (*.ocx);
In this context the term “protection” means realization of two major ideas. The first one is “try before you buy” concept support system (the mentioned concept is the main principle of the shareware marketing method). And the second one is protection of program module machine code from analysis and cracking. As it can be seen, the protection is realized in different, but nevertheless greatly interrelated aspects which are protection of the developer’s economic interests and technical protection of a software product. Later we will consider these ideas in more detail. 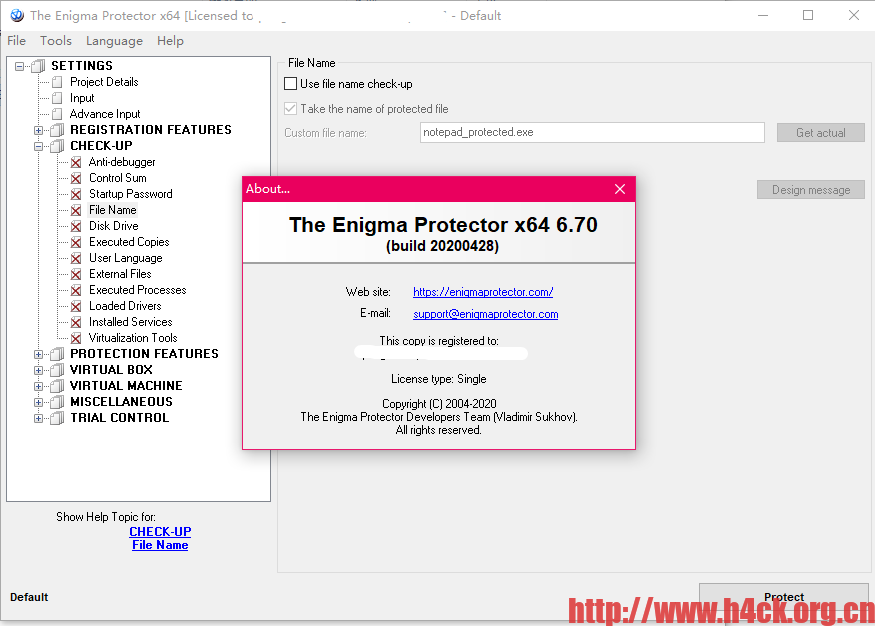
What can The Enigma Protector do?
The Enigma Protector has a hard scheme of registration keys generation:
- comfortable interface for creating and verifying registration keys. You do not need to look for any safe decisions on how to generate registration keys for customers. The Enigma Protector helps you to create keys with a very safe algorithm like RSA with up to 4096-bits key length!
- special Enigma API. Enigma API is a set of special functions to communicate between the module and the Enigma loader. You are able to get full information about registration keys, current trial parameters, etc.
- hardware locking of registration keys. This perfect feature helps you to generate registration keys for a particular computer only! The registration key generated with the hardware locking function enables work only on one PC you have chosen.
- time limited registration keys. If you need to limit the time of usage of a registered version of the module, you will be able to do it, just create a time-limited registration key!
The Enigma Protector has a wide range of features to limit time of module usage:
- executions, days, date, time limitations. The main idea of shareware modules is “try before you buy”. The customer should see how the application works and what features it has, let’s show these features but do not forget to limit usage time to increase motivation to buy application.
- system clock control. This feature is used to control system clock reversing. It helps you to avoid dishonest customers.
The Enigma Protector has a lot of features to make your software resistant to cracking:
- anti-debugger tricks. Debuggers are the special tools that allow you to reverse source machine codes of the executed module. All reverse engineers use these tools to understand how your module works or how the module protection works. Using this feature helps to avoid simultaneous execution of the protected module with debug tools.
- control sum checking. Control sum is special data which helps to understand if the data region is modified or not. Every crack (removing of protection etc.) needs to modify some of machine code region. The Enigma Protector is able to check if the sources are modified and an alert is made. The Enigma Protector checks not only machine codes of the protected module, but also own sources!
- set startup password. Sometimes you need to limit count of users who are using protected module to a particular group, startup password feature is the most safe decision.
- any additional features to check number of simultaneously executed copies of the protected module, file name of the module, disk type where the module is executed.
- checkup of external files. If your application package contains any other files except the main protected executable module you may use this feature to control these files against modifications.
- checkup of executed processes. This feature is used for checking if some files/processes are executed. It is performed by checking of module file name, process windows text or class. This may help to avoid execution of protected module if any debuggers/screencaptures/monitores are executed.
- checkup of installed services.
- checkup of Windows version.
- checkup of Virtual Machines. If the file is executed under Virtual Machine (VMWare, Virtual PC etc) the execution is terminated.
- hard modifications of import table of the executable. Nobody will know what import libraries your module uses.
The Enigma Protector has features to help the programmer to add beautiful things into existing module without writing any additional sources strings:
- splash screen. Add splash screen to the module startup. Choose your own picture to be shown when the module starts.
下载链接:
89 comments
thank you
thank you
好好
谢谢
谢谢


抱歉,我丢失了链接
thanks
thanks for you
ok. thank
Gracias por esta app
ty ty ty
nice
nice
Good
Enigma Protector 包括一系列独特的功能,旨在保护可执行文件免遭非法复制、黑客攻击、修改和分析? 认真对软件学习学习一下。
download porfavor!
<3
ive been looking everywhere for this
linkpls
link pls
NICE!
very good
good job
Exelente espero sirva